5 Reasons Banks and Credit Unions Automate User Access Reviews with Access Auditor
Executive Summary
Top banks and credit unions automate their User Access Reviews (UAR) with Access Auditor. The UAR process is a critical regulatory requirement that frequently becomes a manual, error-prone burden. Access Auditor from Security Compliance Corp (SCC) is a platform designed to navigate the unique complexities of the financial sector. Access Auditor integrates with all core platforms, uses the Fuzzy ID technology to link disparate user accounts, and enables exception-based role reviews. This paper will present the top five reasons why financial institutions use Access Auditor to stop the spreadsheet rodeo and start continuous compliance and proactive risk management.
The Problem With Manual Access Reviews
User access reviews are a cornerstone of regulatory compliance for financial institutions. Guidance from FFIEC, requirements under SOX (Sarbanes-Oxley), and safeguards mandated by GLBA (Gramm-Leach-Bliley Act) all emphasize the need for:
- Periodic User Access Certification
- Strong Identity Controls
- Risk-Based Access Review Processes
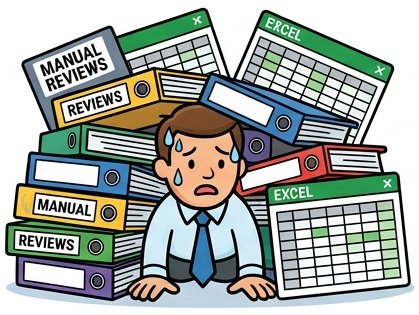
However, many financial companies are using the “spreadsheet rodeo” to reconcile disconnected data from dozens of legacy systems. This manual approach is both labor-intensive and a security and audit risk. Approvers are overwhelmed by thousands of lines in an Excel sheet and resort to rubber-stamping approvals, leaving the door open for privilege creep and unauthorized access.
Access Auditor modernizes user access reviews and delivers automation, accuracy, and risk intelligence.
5 Strategic Reasons to Automate with Access Auditor
Reason 1: Seamless Integration Across Every Banking Core
Unlike generic Identity Governance (IGA) tools, Access Auditor was built to handle the technical idiosyncrasies of the financial sector. Most banking environments are a hybrid of modern cloud services and legacy core platforms like Fiserv, FIS, and Jack Henry.
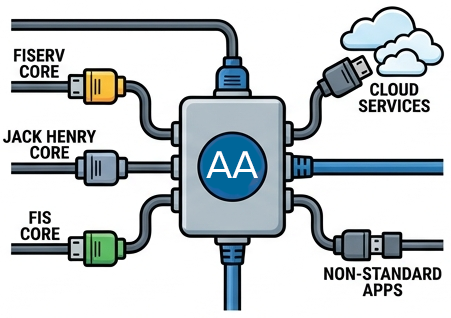
- The Problem: These core systems often produce non-standard reports or flat files that don’t talk to traditional security software.
- The Access Auditor Advantage: Access Auditor is designed to work with every major banking core, as well as secondary non-standard applications and all major cloud providers. By centralizing this into an Identity Warehouse, Access Auditor gives you a 360-degree view of user permissions across the entire enterprise, from on-premise databases to cloud-based teller applications.
In these situations, the true underlying risks may remain hidden while performing a user access review, undermining the very purpose of identity governance.
Regulatory Alignment
- FFIEC IT Examination Handbook: Requires institutions to maintain visibility across all systems impacting financial reporting and operations
- SOX: Demands complete coverage of systems tied to financial controls
- GLBA: Requires institutions to protect customer data across all platforms
Reason 2: Link Disparate Identities With the Fuzzy ID
One of the most persistent hurdles in banking audits is the lack of a common identifier. Many legacy applications do not provide an email address or a consistent Employee ID in their exported reports, making it nearly impossible to know if “JSmith_99” in the core is the same “John Smith” in Active Directory.
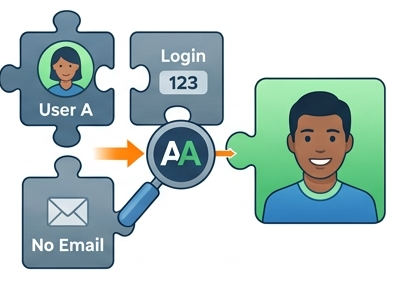
- Proprietary Fuzzy ID Technology: Access Auditor utilizes advanced Fuzzy ID matching algorithms to link disparate accounts automatically.
- Risk Mitigation: By correlating users based on name, department, and other metadata, Fuzzy ID eliminates “orphan accounts”, login accounts left behind from terminated users. Access Auditor provides a clear picture of exactly who has access to what.
Regulatory Alignment
- FFIEC: Emphasizes accurate user identification and accountability
- SOX: Requires traceability of user activity to individuals
- GLBA Safeguards Rule: Mandates control over who has access to customer data
Reason 3: Automate Reviews with a Flexible Workflow Engine
Manual UARs often fail because the review tasks are sent to the wrong people. Sending a 500-page report to a Department Head who only understands 10% of the application leads to ineffective access reviews.
- Flexible Workflow Engine: Access Auditor allows you to define complex assignment criteria. You can automatically route reviews based on:
- Supervisor/Manager: Typical workflow for larger enterprises where the manager reviews access of their direct reports.
- Application Owner: Sometimes the owner(s) of the application can attest to the user access of everyone in a system.
- High-Risk Permissions: High-risk privileges are often reviewed by someone different, such as an application owner of the information security team.
- Custom User Attributes: Sometimes a person reviews user records “just because” they are tasked with being the approver.
- The Result: Regardless of your requirements and use cases, Access Auditor has an incredibly flexible workflow engine so you do not need to change your process. This ensures that the most qualified individual is making the decision, turning a checkbox exercise into a meaningful security control.
Regulatory Alignment
- SOX: Requires documented, repeatable control processes
- FFIEC: Calls for formalized access review procedures
- GLBA: Requires administrative controls to manage access
Reason 4: Identify Risks with Role-Based Exception Reviews
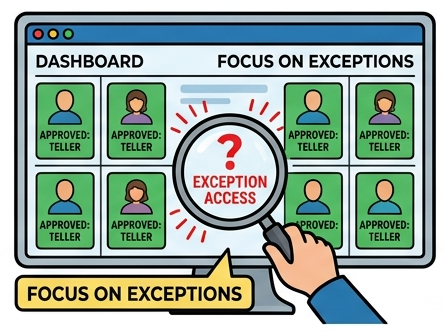
The traditional way of reviewing every single permission for every single employee is unsustainable. Security Compliance Corp (SCC) introduces a smarter way through the Role Manager module.
- Enterprise Role Mining: Access Auditor discovers standard roles within your organization such as Teller, Loan Officer, or Branch Manager. Using data analytics, the Role Manager discovers common profiles and suggests enterprise role definitions to begin the RBAC project.
- Focusing on the Exceptions: With the Role Manager, user access reviews become role-based reviews. Instead of verifying 40 standard permissions that every Teller needs, the reviewer only sees the pre-approved roles and the anomalies, those permissions not part of one of the user’s roles. Many banks and credit unions will go further and launch their user access reviews as exception-only reviews. If permissions are assigned by your job code, you only need to review the exceptions to your roles.
- Speed & Accuracy: This review by exception model reduces the volume of review items by up to 90%, allowing your team to identify and remediate high-risk privilege creep in minutes rather than weeks.
Regulatory Alignment
- FFIEC: Promotes least privilege and role-based access controls
- SOX: Requires control over excessive or inappropriate access
- GLBA: Encourages limiting access to only what is necessary
Reason 5: Data-Driven Decisions with Access Intelligence
To move beyond simple Yes/No approvals, SCC’s Access Intelligence provides real-time risk analytics directly to the reviewer. By highlighting anomalous access and providing a risk score for specific permissions, the system helps approvers make intelligent, data-driven decisions. This transforms the UAR from a checkbox exercise into a proactive security tool.

- Actionable Risk Analytics: SCC’s Access Intelligence embeds risk scoring directly into the review interface.
- Intelligence During the Review: If a user has access that is statistically anomalous compared to their peers, the system flags it. Approvers are empowered with data-driven insights, allowing them to make intelligent decisions based on “peer group analysis” and “high-risk permission tagging” rather than guesswork.
Regulatory Alignment
- FFIEC: Requires risk-based access controls and monitoring
- SOX: Focuses on preventing fraud via separation of duties
- GLBA: Requires ongoing risk assessment and mitigation
Proven Success: Real-World Results
First National Bank: Automating User Access Reviews Using the Fuzzy ID
FNB needed to automate their labor-intensive and manual entitlement review process. With approximately 4500 employees and no common login ID format, access reviews became a significant resource burden.
Access Auditor delivered success by providing FNB significant time savings, improvements in finding and removing orphaned user accounts, and positive feedback from internal and external auditors.
The Bancorp: Automate User Access Reviews at Scale
The Bancorp needed to automate the entitlement review process for managers and streamline a very labor-intensive process of managing data from disparate systems. Some employees had over 300 disparate access privileges. The collation, management, and analysis was extremely unwieldy for manual processing.
Access Auditor automated the entire re-certification process. The Bancorp can now launch entitlement reviews with the push of a button. The Bancorp had an overwhelming success with their user community. FDIC examiners and auditors recognized Access Auditor as a major enhancement for the overall security program.
Conclusion: Transform Your Compliance Strategy
In an era where identity is the new perimeter, traditional approaches to access management are no longer sufficient. Security Compliance Corp’s Access Intelligence offers a powerful solution to the complex challenge of user access risk. By delivering customizable analytics, precise risk identification, and seamlessly integrated workflows, Access Intelligence empowers organizations to achieve true identity governance that is secure, compliant, and efficient.
See Access Auditor in Action
Contact us today for a demo on how to automate your user access reviews in a matter of days.
