Financial Services Automate User Access Reviews with Access Auditor
Financial institutions across the industry are modernizing their User Access Review (UAR) programs with Access Auditor. UARs are essential for meeting regulatory expectations, yet they often become manual, inconsistent, and error‑prone. Access Auditor, developed by Security Compliance Corp (SCC), is purpose‑built to address the identity governance challenges unique to financial services. It integrates with diverse systems, uses Fuzzy ID technology to unify fragmented user identities, and supports exception‑based role reviews. This paper outlines the five key reasons financial institutions are replacing spreadsheet‑driven reviews with automated, continuous compliance and proactive risk management.
The Problem With Manual Access Reviews
User access reviews are a foundational control across the financial sector. Regulatory frameworks such as FFIEC guidance, SOX requirements, and GLBA safeguards all emphasize:
- Periodic access certification
- Strong identity and entitlement controls
- Risk‑based review processes
However, many institutions still rely on spreadsheets to reconcile user data from numerous legacy and modern systems. This manual approach is slow, inconsistent, and introduces significant security and audit risk. Reviewers often face thousands of entitlements with little context, leading to superficial approvals and increased exposure to privilege creep.
Access Auditor replaces this outdated process with automation, accuracy, and actionable risk intelligence.
5 Strategic Reasons to Automate with Access Auditor
1. Seamless Integration Across All Financial Systems
Financial institutions operate complex environments that blend legacy platforms, cloud services, and specialized line‑of‑business applications. Generic identity governance tools often struggle to interpret the non‑standard data formats produced by these systems.
The Challenge: Many financial platforms generate flat files or proprietary reports that traditional security tools cannot easily process.
The Access Auditor Advantage: Access Auditor is engineered to ingest data from a wide range of financial systems, including core processing platforms, loan systems, trading systems, payment applications, and cloud services. Its Identity Warehouse consolidates this information into a single, comprehensive view of user permissions across the enterprise.
Without this visibility, hidden risks can persist undetected, undermining identity governance efforts.
Regulatory Alignment:
- FFIEC: Requires visibility across systems supporting financial operations
- SOX: Mandates complete coverage of systems tied to financial reporting
- GLBA: Requires protection of customer data across all platforms
2. Link Disparate Identities with Fuzzy ID
A recurring challenge in access reviews is the lack of a consistent identifier across systems. Many legacy or specialized applications do not include email addresses or standardized employee IDs, making it difficult to determine whether accounts belong to the same individual.
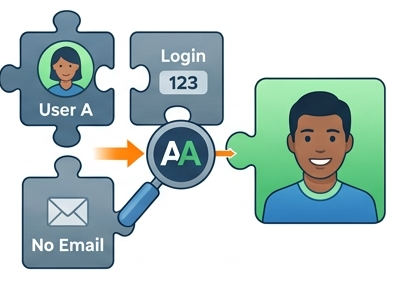
Fuzzy ID Technology: Access Auditor uses advanced matching algorithms to automatically correlate user accounts across systems.
Risk Reduction: By linking accounts based on names, departments, and other metadata, Fuzzy ID identifies orphaned or abandoned accounts, often belonging to former employees or contractors, and provides a unified view of user access.
Regulatory Alignment:
- FFIEC: Stresses accurate user identification
- SOX: Requires traceability of user activity
- GLBA: Mandates control over access to customer information
3. Automate Reviews with a Flexible Workflow Engine
Manual UARs often fail because review tasks are routed to individuals who lack the context to evaluate them. Sending massive reports to department heads or managers who understand only a fraction of the application leads to ineffective reviews.
Flexible Workflow Engine: Access Auditor allows institutions to define sophisticated routing rules, including:
- Manager‑based reviews: Supervisors attest to access for their direct reports
- Application‑owner reviews: System owners validate access across their applications
- High‑risk entitlement reviews: Sensitive permissions can be routed to security or application specialists
- Custom attribute‑based routing: Reviews can be assigned based on any relevant user metadata
The Outcome: Access Auditor adapts to your existing processes rather than forcing you to change them. This ensures that the most knowledgeable person evaluates each access item, turning UARs into meaningful security controls.
Regulatory Alignment:
- SOX: Requires repeatable, documented control processes
- FFIEC: Calls for formalized access review procedures
- GLBA: Requires administrative controls for managing access
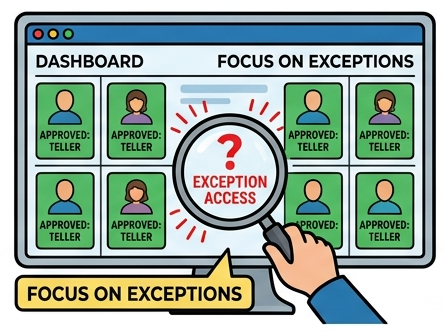
4. Identify Risks with Role‑Based Exception Reviews
Reviewing every entitlement for every user is no longer practical. SCC’s Role Manager module introduces a more efficient, intelligence‑driven approach.
Enterprise Role Mining: Access Auditor analyzes entitlement patterns to identify common roles — such as Teller, Underwriter, Analyst, Advisor, or Claims Specialist — and recommends standardized role definitions.
Exception‑Based Reviews: Instead of reviewing all permissions, reviewers focus only on deviations from approved roles. Many institutions adopt exception‑only reviews, where only outliers require attention.
Speed and Accuracy: This model can reduce review volume by up to 90%, enabling teams to identify and correct privilege creep quickly.
Regulatory Alignment:
- FFIEC: Encourages least‑privilege and role‑based access
- SOX: Requires control over excessive access
- GLBA: Supports limiting access to what is necessary
5. Data‑Driven Decisions with Access Intelligence
To move beyond simple approval checkboxes, SCC’s Access Intelligence provides real‑time risk insights directly within the review interface.

Actionable Analytics: Risk scoring highlights high‑risk entitlements and anomalous access patterns.
Intelligence During the Review: If a user’s access differs significantly from peers in similar roles, the system flags it. Reviewers gain context through peer‑group analysis and high‑risk permission tagging, enabling informed decisions rather than guesswork.
Regulatory Alignment:
- FFIEC: Requires risk‑based access controls
- SOX: Focuses on preventing fraud and enforcing separation of duties
- GLBA: Requires ongoing risk assessment
Strengthen Your Identity Governance Program
As identity becomes the new security perimeter, traditional access review methods are no longer adequate. SCC’s Access Auditor and Access Intelligence provide a modern, integrated solution for managing user access risk. With customizable analytics, precise risk identification, and automated workflows, financial institutions can achieve true identity governance that is secure, compliant, and operationally efficient.
Successful Financial Customers









